Computing & Technology
View AllRecapturing early-internet whimsy with HTML
Modern forms of coding make most websites feel like commercial transactions. The HTML Energy movement aims to bring back the joys of the early days.
How to Use AI to Talk to Whales—and Save Life on Earth
With ecosystems in crisis, engineers and scientists are teaming up to decipher what animals are saying. Their hope: By truly listening to nature, humans will decide to protect it.
Everyone Wants Ukraine’s Battlefield Data
The scale of the fighting and the sheer number of weapons systems and high-tech sensors deployed have created a vast amount of data about how battles are fought and how people and machines behave under fire. For businesses that want to build the next generation of weapons, or train systems that will be useful in future conflicts, that is a resource of incalculable value.
The AI Detection Arms Race Is On
And college students are developing the weapons, quickly building tools that identify AI-generated text—and tools to evade detection. … There’s no stopping AI writing; the only option is to work with it.
New Threats to Society from Free-Speech Social Media Platforms
Understanding emerging threats from social media platforms.
What OpenAI Really Wants
The young company sent shock waves around the world when it released ChatGPT. But that was just the start. The ultimate goal: Change everything. Yes. Everything.
8 Google Employees Invented Modern AI. Here’s the Inside Story
They met by chance, got hooked on an idea, and wrote the “Transformers” paper—the most consequential tech breakthrough in recent history.
Inside the messy ethics of making war with machines
AI is making its way into decision-making in battle. Who’s to blame when something goes wrong?
Andrew Ng: How to be an innovator
Tips for aspiring innovators on trying, failing, and the future of AI.
2023 Innovator of the Year: As AI models are released into the wild, Sharon Li wants to ensure they’re safe
Li’s research could prevent AI models from failing catastrophically when they encounter unfamiliar scenarios.
This startup has engineered a clever way to reuse waste heat from cloud computing
Heata is now using these busy servers to heat water for homes.
CyberSecurity
View All80 years later, GCHQ releases new images of Nazi code-breaking computer
GCHQ unveils new docs on Colossus, a 1943 marvel that let allies “read Hitler’s mind.”
Resources for Cybersecurity Clinics
CISA released this Resource Guide for Cybersecurity Clinics to outline ways CISA can partner with and support cybersecurity clinics and their clients.
CISA and NSA Release Cybersecurity Information Sheets on Cloud Security Best Practices
Cybersecurity Information Sheets (CSIs) to provide organizations with recommended best practices and/or mitigations to improve the security of their cloud environment(s)
CISA Releases Microsoft 365 Secure Configuration Baselines and SCuBAGear Tool
CISA has published the finalized Microsoft 365 Secure Configuration Baselines, designed to bolster the security and resilience of organizations’ Microsoft 365 (M365) cloud services.
How to Be More Anonymous Online
Being fully anonymous is next to impossible—but you can significantly limit what the internet knows about you by sticking to a few basic rules.
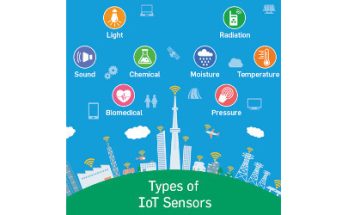
Standards to Secure the Sensors That Power IoT
Yet as IoT adoption increases, IoT sensors and devices also are becoming more popular targets for cybercriminals.
A Turning Point for Cyber Insurance
Going forward cyber-insurance providers will thrive by succeeding in: rewarding security; generating knowledge; and punishing insecurity.
CISA Cybersecurity Strategic Plan
The Cybersecurity and Infrastructure Security Agency’s (CISA) 2023-2025 Strategic Plan is the agency’s first, comprehensive strategic plan since CISA was established in 2018. This is a major milestone for the agency.
CISA Develops Factsheet for Free Tools for Cloud Environments
CISA has developed and published a factsheet, Free Tools for Cloud Environments, to help businesses transitioning into a cloud environment identify proper tools and techniques necessary for the protection of critical assets and data security.
The Cybersecurity Dilemma: Hacking, Trust and Fear Between Nations
Why do nations break into one another’s most important computer networks? There is an obvious answer: to steal valuable information or to attack. But this isn’t the full story.
Lamboozling Attackers: A New Generation of Deception
Imagine a world in which developers and operators of systems exploit attackers as much as attackers exploit defenders. By leveraging system-design knowledge and modern computing to deploy deception environments, software engineering teams can successfully bamboozle attackers for fun and profit while deepening systems resilience.
Climate
View AllThe Carbon Footprint of Artificial Intelligence
Looking for ways to cut the release of greenhouse gases attributable to AI use, at a time that usage is very likely to grow.
The Catholic cartographer who wants to help the church fight climate change
The Catholic Church is one of the world’s largest landowners. Using public data and GIS, Molly Burhans is trying to make it a better steward.
The Trillion-Dollar Auction to Save the World
Ocean creatures soak up huge amounts of humanity’s carbon mess. Should we value them like financial assets?
Let Us Not Put All Our Eggs in One Basket
But what about the overall environmental impacts of this growing infrastructure and the huge number of short-lived devices connected to it, or the indirect impacts on other sectors?
Mapping California’s ‘Zombie’ Forests
In California’s ‘zombie’ forests, conifers have become mismatched to a warming climate.
Our House Is On Fire: The Climate Emergency and Computing’s Responsibility
We will most likely never do better than a best guess at computing’s carbon footprint, but given uncertainties it would be safer and more responsible to act on the assumption that higher estimates could be closer to the truth—especially since the pace of warming has exceeded our expectations at every point. But in big-picture terms, the difference between 1.8% and 3.9% does not fundamentally change our mission: computing’s emissions must be reduced urgently and drastically. How are we going to achieve this?
Extreme Heat Is a Disease for Cities. Treat It That Way
The “urban heat island effect” creates extra-hot temperatures that kill. But cities can prescribe powerful treatments, like green spaces and reflective roofs.
Hidden beneath the surface
Digging deep into a humble lake in Canada, scientists found a spot on Earth like no other — and a record that could redefine our history of the planet
Hurricane Ian Is a Warning From the Future
Tropical storms are increasingly likely to batter the US as oceans warm—and will continue to wreak havoc so long as climate change remains unaddressed.
The Desert’s Fragile Skin Can’t Take Much More Heat
Climate change and human activity are destroying the layers of fungi, lichen, and bacteria that protect deserts from erosion.
Weather | Snow | Utah
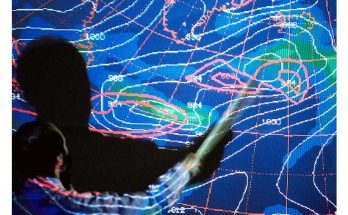
View AllWeather forecasting is having an AI moment
Using AI to predict weather has a big advantage: it’s fast. Traditional forecasting models are big, complex computer algorithms based on atmospheric physics and take hours to run. AI models can create forecasts in just seconds.
New AI systems could speed up our ability to create weather forecasts
They could also help to make them more accurate.
National Weather Service Glossary
The National Weather Service glossary contains information on more than 2000 terms, phrases and abbreviations used by the NWS.
DeepMind AI accurately forecasts weather — on a desktop computer
The machine-learning model takes less than a minute to predict future weather worldwide more precisely than other approaches.
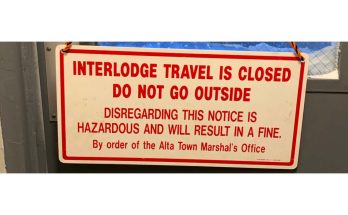
Avalanches in Big & Little Cottonwood Canyon Early April 2023
During the last week of March and first week of April, Big & Little Cottonwood Canyons saw an epic snow cycle the likes of which have never been seen before. Little Cottonwood Canyon (“LCC”) closed due to avalanche danger on Sunday April 2, 2023. The canyon generally did not open again until Saturday April 8. (There were two brief periods when the canyon was open to the public to downhill travel only, so that people who needed/wanted could leave. Otherwise, the general public was prohibited from going up or down the canyon during the period April 1-8.
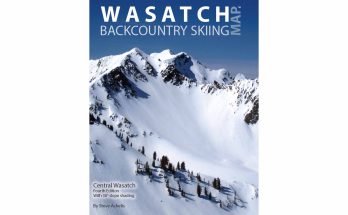
Wasatch Backcountry Skiing Map, 4th Ed.
The Wasatch Backcountry Skiing Map is a full-color paper map that compliments the website, Android app, and iOS app. The map includes the names of almost 1,000 backcountry locations in the Central Wasatch.
Winter Storm Elliott – December, 2022
The United States was hit by historically cold and windy Winter weather with a rare mid-latitude mid-continent cyclone, one that would undergo a process of rapid intensification called Bombogenesis, or Bomb Cyclogenesis. The event was termed “Winter Storm Elliott.” This …
A History of Avalanche Mitigation in the Cottonwood Canyons
Big and Little Cottonwood Canyon roads carve between steep mountains that are prone to avalanches in the winter. In fact, 57% of the 9-mile Little Cottonwood Canyon Road is in an avalanche runout zone. Still, recreationalists, residents, and canyon employees need to transport themselves up and down these canyons regularly and as safely as possible.
Web Resources
View AllThe Design of Everyday Things
“This is a starter kit for good design. It is intended to be enjoyable and informative for everyone: everyday people, technical people, designers, and nondesigners.”
Color Blind Accessibility Manifesto
A study conducted in 2021 by Web Accessibility In Mind illustrated that 83% of the Internet’s top one million homepages failed to meet minimum color contrast requirements. That means about 860,000 of the most visited pages on the Internet aren’t designed with people with Color Vision Deficiency in mind.
Flexbox Tutorial by Sean Fioritto
This is an interactive video intro to flexbox and is comprised of 5 sections that walk through various parts of flexbox.
F.B. Purity – Clean Up and Customize Facebook
F.B. Purity is a browser extension / add-on that lets you clean up and customise Facebook. It filters out the junk you don’t want to see, leaving behind the stories and page elements you do wish to see. The list of story types that FBP hides is customizable to your taste.
WPBeginner – Beginner’s Guide for WordPress
At WPBeginner, our main goal is to provide cutting-edge helpful WordPress tutorials that are easy to understand for small businesses, bloggers, and non-techy WordPress website owners.
Auditing For Accessibility Problems With Firefox Developer Tools
The Firefox 70 Accessibility Inspector is an auditing facility to help identify and fix many common mistakes and practices to help improve site accessibility.
Internet Archive Wayback Machine
The Wayback Machine is a digital archive of the World Wide Web and other information on the Internet. It was launched in 2001 by the Internet Archive, a nonprofit organization based in San Francisco, California, United States.